Introduction
The Digital Signatures Act 1997 (Act 562) (“DSA”) establishes a secure, legally recognised framework for executing agreements in Malaysia using cryptographic digital signatures. Unlike basic electronic signatures, a digital signature under the DSA must be created using a valid digital certificate issued by a Licensed Certification Authority (LCA), ensuring authenticity, integrity, and non-repudiation of the signed document.
This article outlines the statutory requirements under the DSA for a digital signature to be legally binding, explains the step-by-step execution process, identifies the duties of signers and recipients, and highlights verification and record-keeping best practices. It also compares DSA-compliant digital signatures with general electronic signatures under the Electronic Commerce Act 2006 (“ECA”), equipping businesses and professionals with the knowledge to choose the right signing method for their legal and commercial needs.
Legal Framework
What is a “digital signature”?
A cryptographic transformation of a message using an asymmetric key pair (private/public key) such that anyone with the message and the signer’s public key can verify (i) the signature was created with the corresponding private key and (ii) the message has not been altered.
When does a digital signature satisfy a legal “signature” requirement?
If all the following are fulfilled/true:-
- the signature verifies to the public key in a valid certificate issued by a licensed certification authority (LCA);
- the signer affixed it with the intention to sign; and
- the recipient has no knowledge/notice that the signer breached subscriber duties or doesn’t rightfully hold the private key. (DSA – Section 62(1)). A document signed accordingly is as binding as a handwritten signature (Section 62(2)).
Effects in law and evidence
If an agreement bears in its entirety a qualifying digital signature, it is deemed “written” (Section 64) and an original (Section 65). Courts apply helpful presumptions (Section 67), and a certificate from an LCA operates as an acknowledgement of the signature (Section 66).
Who licenses and oversees CAs?
The Malaysian Communications and Multimedia Commission (MCMC) performs the Controller’s role post-amendment. The Digital Signature Regulations 1998 require a public register and repositories and empower the Controller to issue guidelines on trustworthy systems, security, reliance limits and audits.
Licensed Certification Authorities (examples)
Market references and LCA repositories commonly list Pos Digicert Sdn Bhd, MSC Trustgate.com Sdn Bhd, Telekom Applied Business Sdn Bhd, and Raffcomm Technologies Sdn Bhd as LCAs under the DSA. (Always check current licensing status with MCMC or the LCA’s repository/CPS.)
Important distinction: The ECA 2006 recognises simpler “electronic signatures” for most commercial transactions but excludes certain instruments (e.g., powers of attorney, wills/codicils, creation of trusts, negotiable instruments) and situations requiring notarisation/attestation. The DSA’s digital-signature route is separate and more prescriptive, evaluate any other formalities that may still require physical acts.
The execution workflow (practical steps)
A. Prepare the agreement
- Finalise the contract in a format your signing platform can hash and sign without altering content post-signature (PDF is common).
- Add a digital execution clause (model wording below).
B. Enrol with a Licensed Certification Authority (LCA)
- Identity proofing & certificate issuance: the LCA verifies the subscriber and issues a digital certificate (public key + identity), per the LCA’s Certification Practice Statement (CPS).
- Generate/secure your key pair (private key stays under your sole control – see duties below).
C. Sign the document (DSA-compliant)
- Use trusted signing software that integrates your private key and your valid LCA certificate.
- Apply the digital signature to the full document (so that the file “bears in its entirety a digital signature” for Section 64). Consider adding an LCA/recognized timestamp.
- Package/attach the certificate chain (and timestamp token if used).
D. Exchange and verify
- Counterparties (recipients) should verify:
- the signature cryptographically validates to the public key in the signer’s valid LCA certificate;
- the certificate wasn’t suspended/revoked/expired at signing; and
- the file has not been modified since signing.
Note: Reasonable verification supports reliance (see Section 63 on “unreliable” signatures).
- If in doubt, recipients should not rely on and must promptly notify the signer with reasons (Section 63(2)).
E. Post-execution records
- Archive the signed PDF, the verification report, the certificate(s), and any timestamp evidence.
- Keep an activity/audit log (who signed, when, certificate serial numbers).
- Store records in a trustworthy system – LCAs and repositories have 10-year retention rules—mirror that for transaction files.
Duties & risk allocation
Subscriber duties (you, as signer)
- Keep the private key secure; it is your personal property (Sections 43–44). If an LCA holds your private key (e.g., managed HSM), it holds it as fiduciary and may use it only with your prior written approval (Section 45).
- Notify promptly for suspension/revocation on compromise (Part IV Ch.5–6).
Recipient (counterparty)
- Must exercise reasonable reliance—check validity/revocation; otherwise, the recipient assumes the risk of forgery (Section 63).
Licensed Certification Authority
- Warranties, ongoing obligations, and reliance limits apply; repositories bear liability if they fail to publish suspension/revocation promptly (Part IV; Part VI s.68–69).
Verification checklist (for each signed agreement)
- The file cryptographically validates end-to-end.
- The signers’ certificates are LCA-issued and were valid at the signing time.
- No revocation/suspension at or before signing (check CRL/OCSP/repository).
- The signer was intending to sign (execution block, workflow evidence).
- If time is material, include/verify a recognized timestamp.
- Save the verification report, certificate chain, and audit trail with the contract.
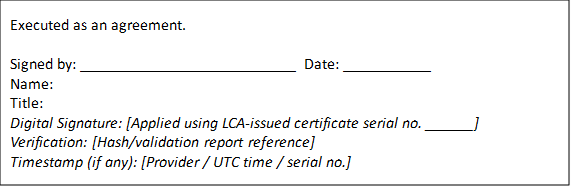
Model “Digital Execution” clause (DSA-focused)
Digital Signatures: Each Party may execute this Agreement by applying a digital signature to an electronic copy of this Agreement using a valid certificate issued by a Licensed Certification Authority under Malaysia’s Digital Signatures Act 1997 (Act 562). A document signed in this manner shall be legally binding and deemed written and original as provided in Sections 62, 64 and 65 of the DSA. Each recipient may rely on a digital signature that verifies to the public key in the signer’s valid certificate unless the recipient has knowledge or notice as described in Section 62(1)(c) or otherwise determines non-reliance under Section 63. Each Party shall maintain appropriate records of its executed copies, verification results, certificate information and any timestamp.
Common pitfalls (and how to avoid them)
Using a generic “e-signature” tool when the deal demands DSA compliance.
If you need the DSA presumptions/effects (e.g., Section 66–67) or a statutory “signature” under Section 62, ensure the solution uses LCA-issued certificates.
Letting certificates lapse before signing is completed.
Verify validity at the time of signature; build an automated OCSP/CRL check into your signing workflow.
Poor key management.
Private keys must remain under the subscriber’s control; if the LCA or a provider holds it, ensure documented fiduciary controls and written approvals
(Section 45).
Mixing up DSA vs. ECA regimes.
Quick comparison: DSA digital signature vs. ECA electronic signature
| Topic | DSA 1997 (Act 562) | ECA 2006 |
| Signature type | Cryptographic digital signature only | Broad electronic signature concept |
| Certificates | Mandatory: issued by licensed CA | Not required |
| Legal effects | Satisfies signature reqs if s.62 conditions met; deemed written/original; evidential presumptions | Validity based on identification, intent, and reliability “as appropriate”; some exclusions |
| Typical use | Higher assurance, regulated workflows, public-sector or high-value deals | General commercial transactions where e-sign is acceptable |
| Exclusions | DSA itself doesn’t list ECA-style exclusions, but other formalities may still apply | Excludes PoA, wills/codicils, creation of trusts, negotiable instruments, and docs needing notarisation/attestation |
Implementation tips (governance & record-keeping)
- Adopt an internal signing policy mapping when to use DSA-compliant signatures vs. ordinary e-signatures.
- Vendor due diligence: obtain the LCA’s CPS, reliance limits, and repository details; confirm timestamp services and validation methods.
- Retention: keep executed agreements and verification artefacts for at least 10 years in a trustworthy system (mirror DSR 1998 record-keeping baselines).
- Training: ensure signers understand their subscriber duties and incident reporting for suspected key compromise.
Template: execution page (signature block)
Conclusion
Executing an agreement with a DSA-compliant digital signature offers the highest level of legal certainty and evidential strength for electronic transactions in Malaysia. By using a certificate issued by an LCA, ensuring proper key management, and verifying signatures before reliance, parties can protect themselves from forgery risks, satisfy statutory “signature” requirements, and preserve enforceability.
However, not all documents can rely solely on electronic methods, and some still require physical execution or attestation under other laws. Businesses should therefore adopt a clear signing policy distinguishing when to use DSA digital signatures versus other forms of execution, and maintain proper records for audit, compliance, and dispute-resolution purposes. Done correctly, DSA-compliant execution modernises contracting while preserving the safeguards of traditional signing.